Cyber Resilience is an organisation’s preparation for business disruption caused by cyber attacks; its ability to recover from these disruptions; and its systemic capability to adapt and grow from each attack it experiences.
Cyber resilience requires that, while organisations strive to prevent incidents, they also understand their internal operating environments and digital ecosystems well enough to develop and deploy processes that:
- Accelerate the detection of successful attacks; and
- Contain and respond to identified attacks.
To achieve Cyber Resilience, companies must also develop the ability to:
- Quickly mitigate and recover from attacks while maintaining essential business operations, even if in a degraded state or using alternative means of delivery;
- Draw upon informal networks within the organisation and across the extended enterprise / supply chain to continue to operate; and
- Identify any local failure inside the organisation that could escalate or cascade and create the organizational capacity to address such failures before they spread.
“A tendency among firms to view cyber threats as a technical problem, rather than an issue which merits Board-level attention given the evolving nature of cyber threats and the key importance of cyber resilience to continuity of financial services.” Record of the Financial Policy Committee of the Bank of England Meetings on the 8 and 15 December 2014.
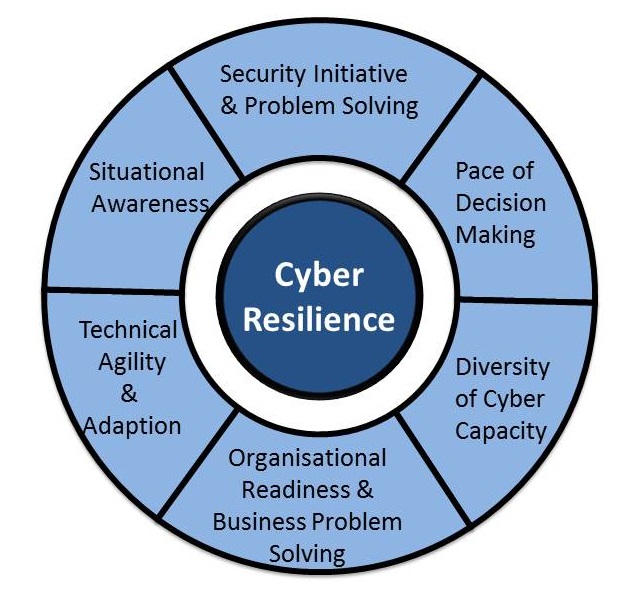
There are six factors that are critical to Cyber Resilience:
| Term | Description |
| Pace of Decision Making | The total time it takes top management and the Board to convene enterprise-wide, ad-hoc decision making groups, provide feedback to these groups; for these groups to make critical decisions; and for the organisation to implement these decisions. This is critically important to ensuring the business can continue to operate in a degraded state. This also requires CISOs to work with broader IT and operations leadership to engage top management, including CEOs and Boards |
Organisational Readiness and Business Problem Solving |
The ability of the organisation to mobilise capable resources and adapt business processes and operations to accommodate unexpected events during a crisis, across the entire enterprise. This clearly requires CISOs to work with broader IT and operations leadership to engage top management, including CEOs |
| Diversity of Cyber Capacity | The redundancy and depth of capacity but also a measure of heterogeneity in the organisation’s digital business and extended enterprises. This focuses on the resilience of the information systems and capabilities to cyber shocks that may target specific systems, technologies or staff. Again, this requires CISOs to work with other IT colleagues to build in flexibility – and, critically, secure necessary investment to go beyond cost minimisation and/or business functionality objectives |
Technical Agility and Adaption |
The ability of the organisation to change technical systems and processes in light of new threats or events. This requires CISOs to work with other IT colleagues to build in flexibility – and, critically, secure necessary investment to go beyond cost minimisation and/or business functionality objectives. This is a key overlap with cyber resistance. |
| Situational Awareness | The understanding of the organisation’s own strengths, assets and weaknesses; as well as likely adversary tactics, targets and capabilities. In this regard it is important that CISOs ensure that organisations have the capability to continually absorb and assess new information, and refresh this understanding. This is a critical overlap with Cyber resistance and underlines the importance of situational awareness to cyber security as a whole. |
Security Initiative and Problem Solving |
The ability of cybersecurity professionals within the business to identify and respond effectively to unexpected situations, including the ability to help the business ‘fail safely’ when attacked. This should be a core competence for CISOs |
This complete blog series can be found here:
2 thoughts on “Cyber Resilience: Part Three What is Cyber Resilience?”
Comments are closed.