In my previous post, I introduced the concept of a ‘Risk Universe’ which I flesh out in more detail here. A Risk Universe provides a comprehensive view of the possible risks we face to aid in categorisation but also to act as a check on the scope of our risk identification exercises to ensure we don’t miss risks that take us by surprise when they occur. A good description of the risk universe concept in operational risk is in Section 6 of this new approach to operational risk [PDF].
Information security or cybersecurity risk is frankly awkward to create a categorisation scheme for as it is a combination of triggers and outcomes that intertwine with so many other operational risks managed by the business. It is useful to consider who may trigger a security risk event, what the range of security risk events could be and their consequences if they do occur.
When assessing the risks we rarely have enough measurable information to be highly confident in our predictions but we can reduce our uncertainty by considering the risk factors that increase or decrease either the likelihood or severity of the risk.
The actual calculations of the risk can be driven by many different methods, the Risk Universe is not where we build risk models but it is where we identify what risk models we may want to build. As a result, a risk universe is compatible with formal methods such as FAIR or the risk quantification methods described by Hubbard and Seiersen in their book.
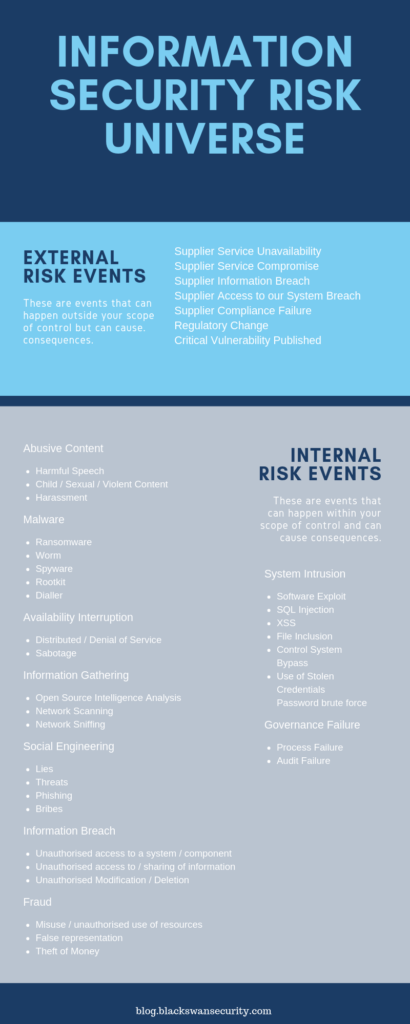
The Information Risk Universe I have developed for my own work is included below. The first graphic describes the sources of risk events and the internal or external risk factors that may impact the frequency by which those risk events occur.

The next graphic describes the risk events themselves, it splits into risk events that can happen within your scope of control and those outside of it. The internal risk events are mostly derived from this ENISA review [PDF] of CSIRT incident taxonomy.
It’s key to understand that a risk event alone is not a risk, it is the combination or one or more sources, one or more risk events and one or more consequences that describe a risk scenario. I posted about how to write a useful risk statement or scenario in my earlier post here.
The final graphic includes the internal and external risk factors that may impact the severity of the consequences caused by a risk occurring and a list of the possible consequences themselves.

I have used this risk universe successfully both in its totality for an enterprise view of security risks and in a cut down form specifically for a supply chain risk assessment approach. I’m sure there are many ways to improve this and I’d be keen to hear comments and improvements from anyone who finds this useful.
UPDATE: I have transformed the risk universe described here into the Open Information Security Risk Universe hosted on Github. This is an editable form that we can change and update, the licence is free. Please read, review, edit and send PRs!
1 thought on “Information Security Risk Universe”
Comments are closed.